What is DSPM? Data Security Posture Management
DSPM finds and protects sensitive data across cloud environments. Learn what Data Security Posture Management does and why it matters.
Expert perspectives on cloud security, compliance, and threat intelligence. Practical guidance for security leaders navigating an evolving landscape.

Supply chain attacks exploit the software you already trust. Learn how SolarWinds, Log4j, and others happened, and how to defend against them.
 Cloud Security
Cloud Security
DSPM finds and protects sensitive data across cloud environments. Learn what Data Security Posture Management does and why it matters.
 Threat Intelligence
Threat Intelligence
After the initial breach, lateral movement is how attackers reach your crown jewels. Learn the techniques they use and how to stop them.
 Best Practices
Best Practices
Zero trust architecture ditches implicit trust for continuous verification. Learn the core principles, key pillars, and practical steps to implement it in your environment.
 Cloud Security
Cloud Security
A cloud misconfiguration is an incorrect or suboptimal security setting in a cloud environment that creates vulnerabilities exploitable by attackers. Learn the top 10 misconfigurations and how to prevent them.
 security
security
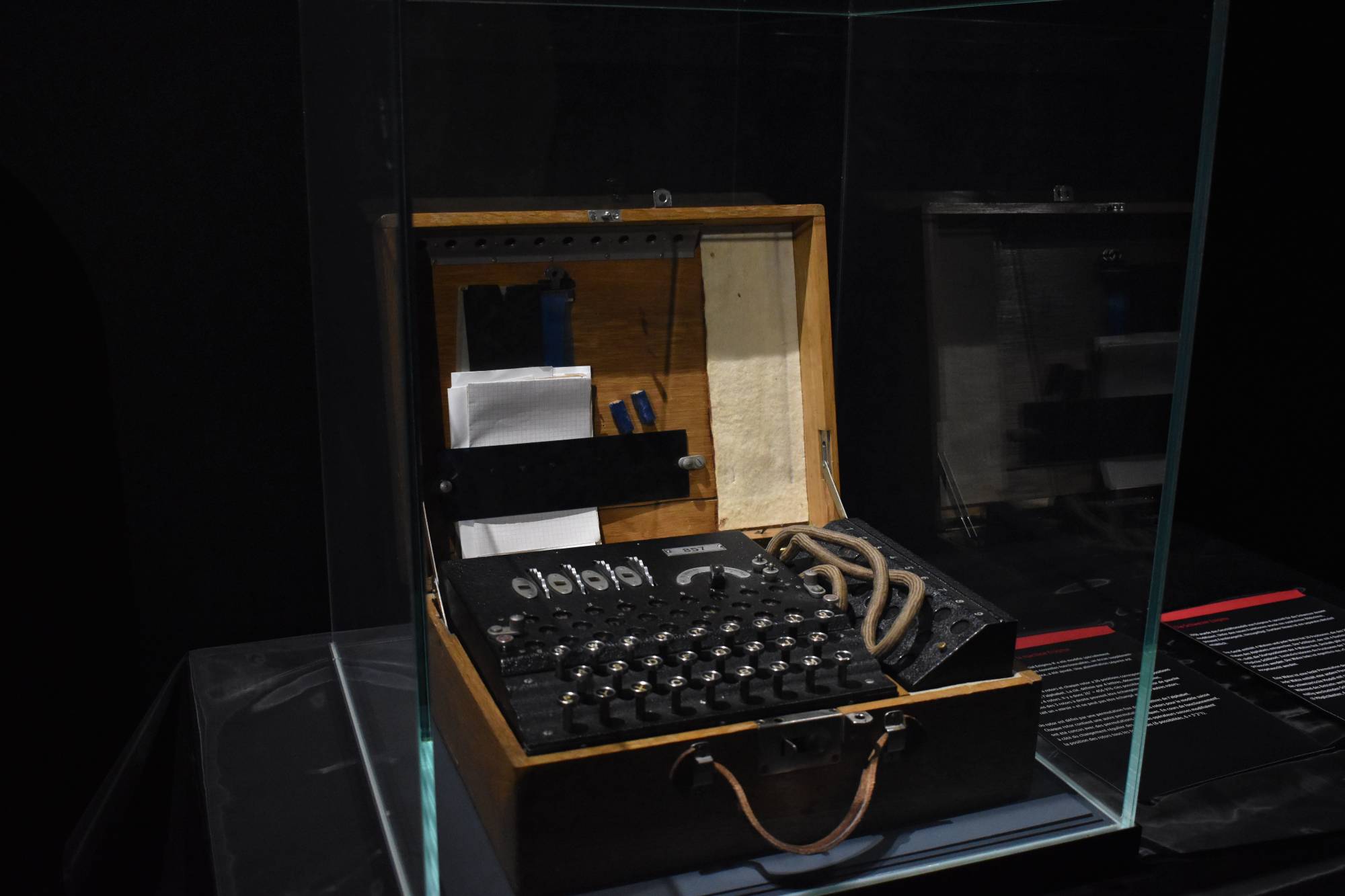
Quantum computers will break RSA and ECC. NIST has finalized the replacement standards. Here's what you need to know and what you should be doing right now.
 Compliance
Compliance
Cloud compliance is the process of ensuring cloud-based systems meet regulatory standards and security policies. Learn about key frameworks like SOC 2, ISO 27001, HIPAA, GDPR and how CSPM helps.
 Threat Intelligence
Threat Intelligence
AI is reshaping cybersecurity from both sides. Here's how attackers are using it against you and how defenders are fighting back.
 Cloud Security
Cloud Security
IaC Security is the practice of scanning and validating Infrastructure as Code templates (Terraform, ARM, Bicep, CloudFormation) for security misconfigurations, compliance violations, and vulnerabilities before deployment.
 Cloud Security
Cloud Security
Cloud Access Security Broker (CASB) is a security enforcement point positioned between cloud service users and cloud applications to monitor activity, enforce security policies, and protect data.
 Cloud Security
Cloud Security
Cloud Infrastructure Entitlement Management (CIEM) is a specialized security category focused on managing and governing identities, permissions, and entitlements across cloud environments.
 Best Practices
Best Practices
Ransomware attacks cost businesses millions. Here are the defense strategies that actually work before you get hit.
 Cloud Security
Cloud Security
Cloud Workload Protection Platform (CWPP) is a security technology focused on protecting running workloads in cloud environments including VMs, containers, serverless functions, and Kubernetes clusters.
 Best Practices
Best Practices
Recovery Point Objective and Recovery Time Objective determine what you can lose and how fast you need to recover. Get them wrong and disasters get expensive.
 Best Practices
Best Practices
Most developers implement OAuth 2.0 wrong. Here are the critical flaws attackers exploit and how to fix them.
 Cloud Security
Cloud Security
Cloud-Native Application Protection Platform (CNAPP) is a unified security platform combining CSPM, CWPP, CIEM, IaC scanning, and container security into a single integrated solution.
 Cloud Security
Cloud Security
Cloud Security Posture Management (CSPM) is a category of cloud security tools that continuously monitor cloud infrastructure for misconfigurations, compliance violations, and security risks across AWS, Azure, and GCP.
 Threat Intelligence
Threat Intelligence
RAM holds secrets disk forensics misses. Learn why memory forensics matters and how tools like Volatility 3 catch malware.
 Best Practices
Best Practices
TPM is the tiny chip that keeps your encryption keys safe from attackers. Here's what it does and why Windows 11 made it mandatory.
 Cloud Security
Cloud Security
Most cloud breaches aren't hacks. They're misconfigurations. Here are the mistakes we see constantly and how to avoid them.
 Best Practices
Best Practices
Fernet encryption makes symmetric encryption in Python dead simple. Learn how to protect sensitive data with AES-128 and HMAC.
 Threat Intelligence
Threat Intelligence
3.4 billion phishing emails hit inboxes daily. Learn how to recognize attacks, protect yourself, and respond if you've been compromised.
 Best Practices
Best Practices
APIs are the backbone of modern apps. They're also where attackers look first. Here's what's going wrong and how to fix it.
 Threat Intelligence
Threat Intelligence
Your network's ARP cache is essential for communication, but it's also a goldmine for attackers. Here's how ARP spoofing works and why you should care.
 Compliance
Compliance
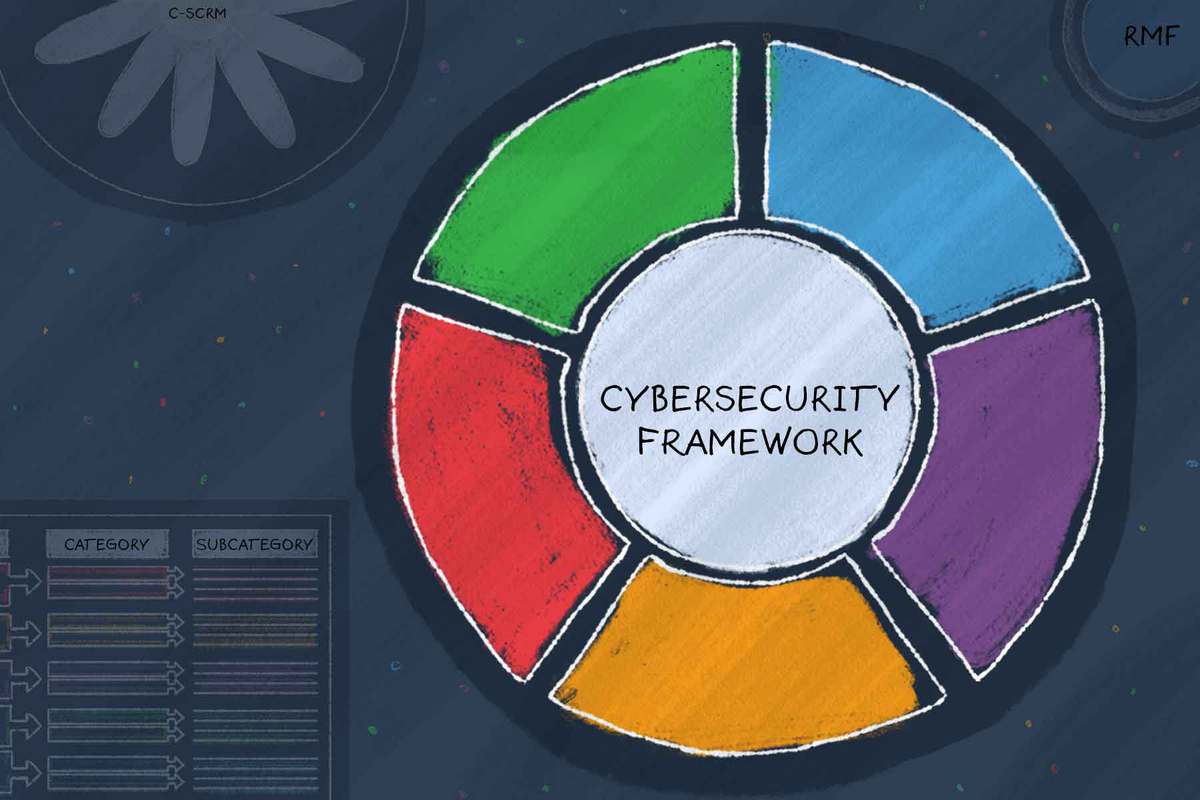
The NIST Cybersecurity Framework gives you a practical structure for security. Here's how to actually use it without drowning in documentation.
 Best Practices
Best Practices
Pentest finds holes. Assessment finds problems. Learn which one your organization needs and when to use each approach.
 Best Practices
Best Practices
Most breaches don't come from genius hackers. They come from skipped updates and lazy passwords. Here's how to fix that.
 Threat Intelligence
Threat Intelligence
Zero-day exploits jumped 46% in 2025. Here's what they are, why attackers love them, and how to protect yourself.
 Best Practices
Best Practices
Certificate pinning stops MITM attacks cold, but it comes with trade-offs. Here's what you need to know before implementing it.
 security
security
Every time you see that padlock icon, TLS is working behind the scenes. Here's what it actually does and why you should care.